Author: rlerner
-

Wordfence and a Secure wp-admin
I use WordFence to protect my site from attacks, many years ago I helped a Redditor secure his site (maybe I’ll blog about it one day). He was using WordFence and it found a nasty local file. I’ve enjoyed it enough to where I spoke about it at a security conference a few years ago.…
-

Using AI to Secure Legacy Software
In 2006, I made the decision to stop writing software for Windows (as much as I did at the time), and move to building web applications. The idea was that, unlike desktop applications where I don’t see my users and can’t do updates easily, in a web app I can. I spoke with my brother,…
-
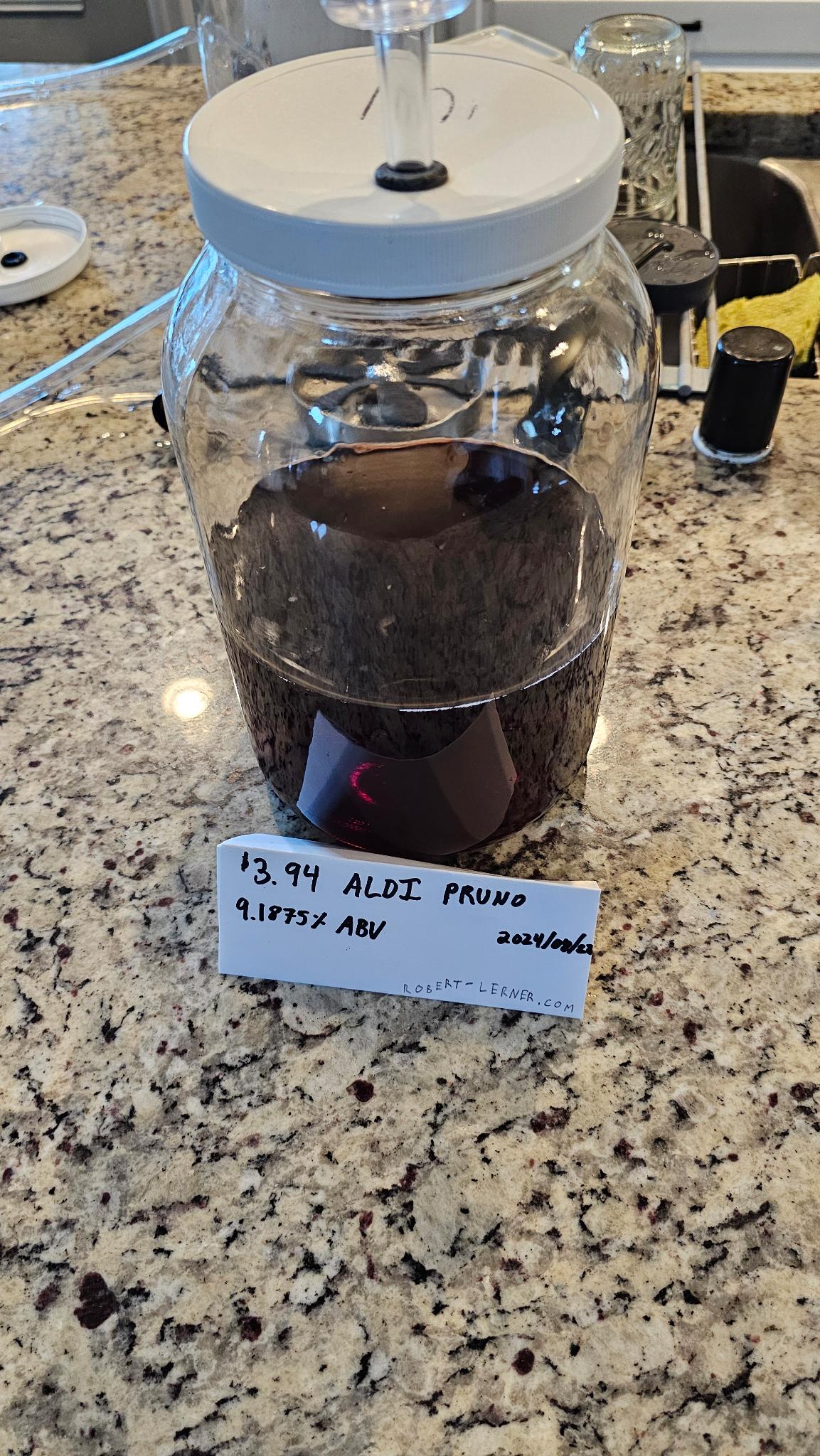
The Saga of Aldi Pruno
This is part two, for the recipe and story, check out this blog. Update: My Friend from the Midwest tried it, said 2.5 out of 5! It’s been several weeks since I made the Aldi Pruno (Prison Wine) — I followed some best practices, such as a proper airlock and sanitation procedures, aerating the wine,…
-

Prison Wine: Why Some Laws are Dumb
It’s August here in Texas, and I decided to write a blog that shouldn’t come out for another few months. I wanted this to come out around a significant date for prohibition, but I don’t have the patience. I got to reckoning with an old Midwestern pal about some good ol’ moonshinin’. The story started…
-
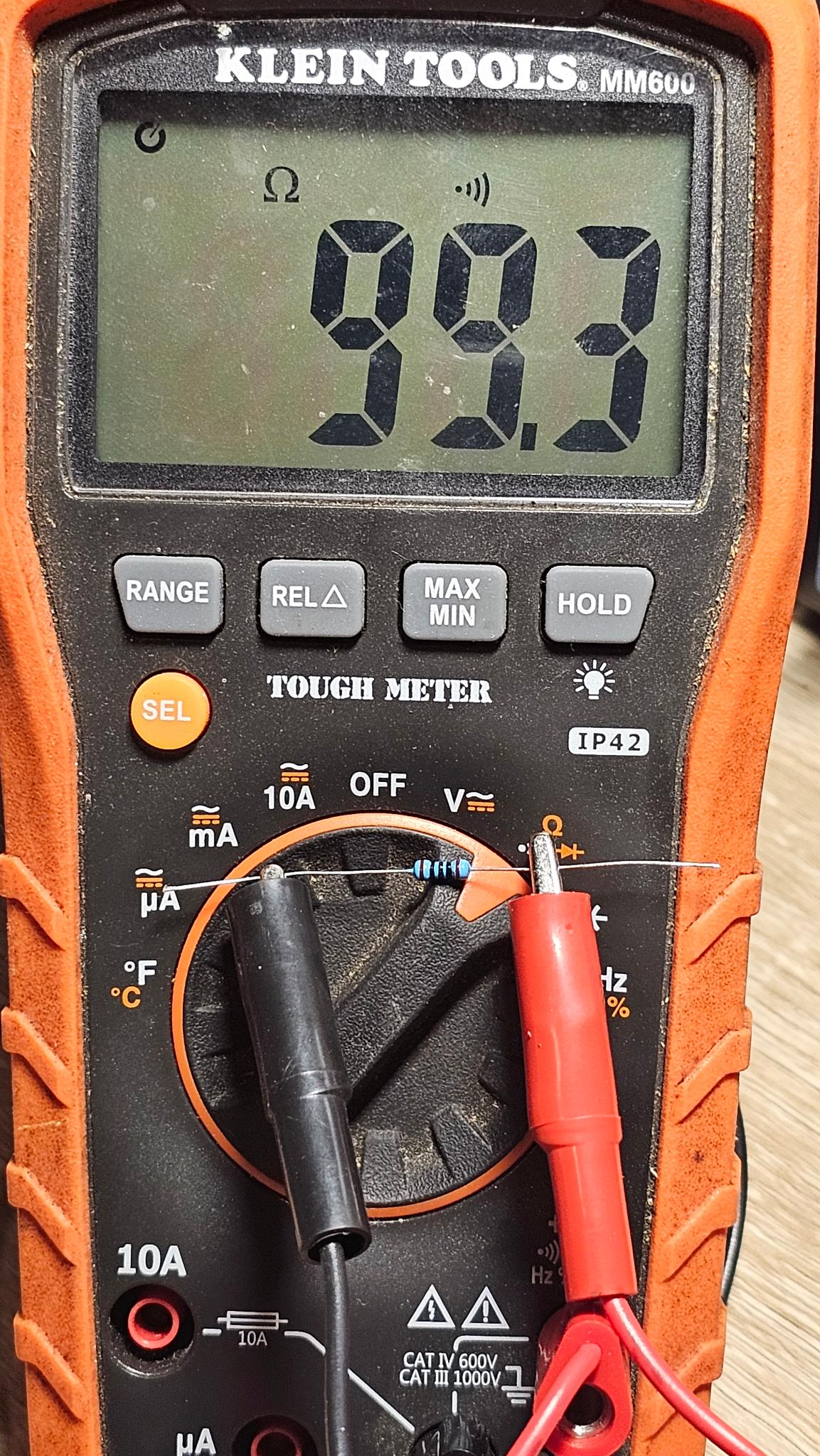
How to Read Resistor Color Codes
-

Impersonating a Police Officer
I don’t normally admit to felonies online, it generally is ill advised and troublesome. So of course, I’m still not going to. Some time ago, I wrote about how I occasionally go for late night walks. Sometimes it is to be healthy, other times it is to run to the store and not drive. One…
-
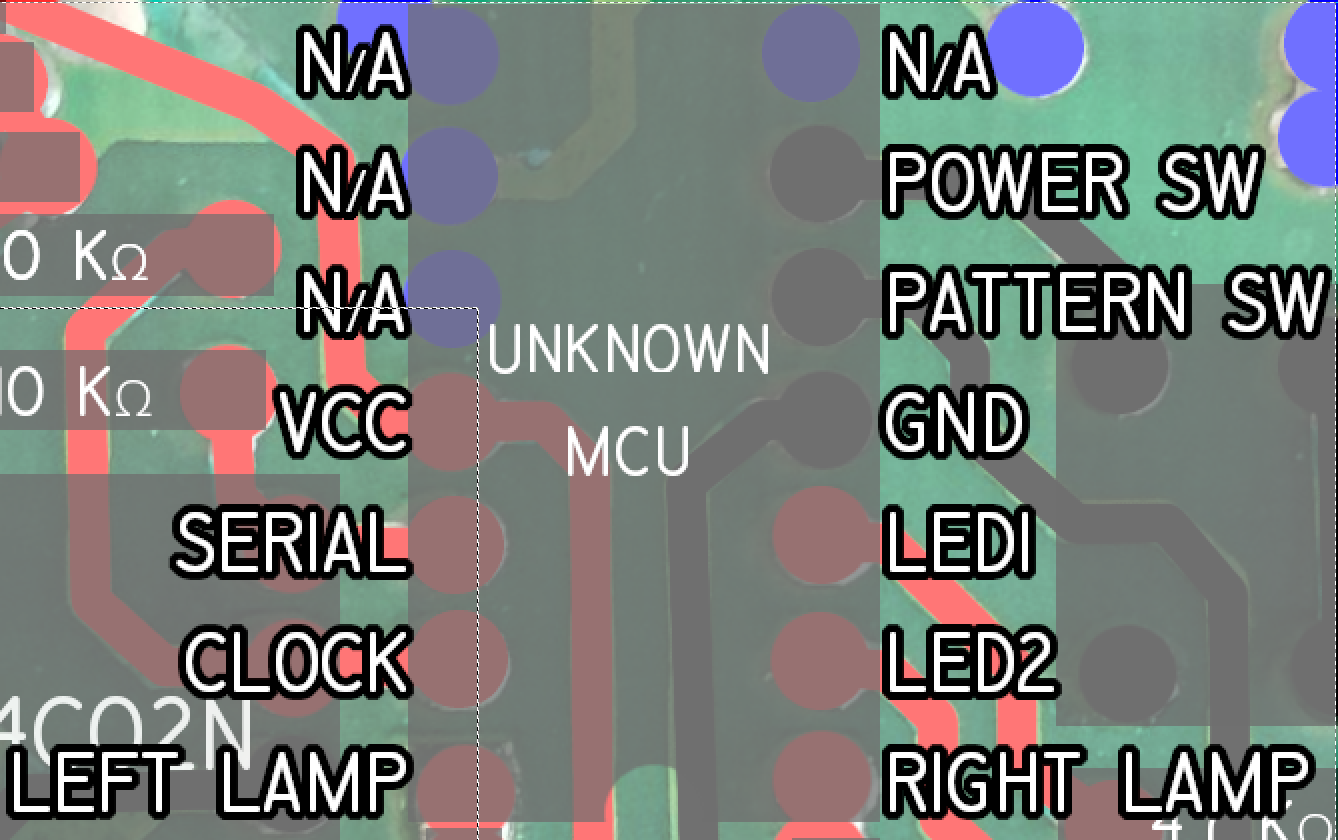
Unmasking Sneaky Microcontroller Part 1: Reverse Engineering the Board
Several years ago, I had added accessory lighting to my tractor since I used it to pull a trailer of stuff around my property and to plow a 200′ long driveway after work. Since after work is usually after 5pm, and during winter it’s dark, I wanted to be seen by all of the meth…
-
I Messed Up…
Just yesterday, I posted a blog about spying on chip communications. In there, I included a little tidbit that I “deep fried” here. Now, I thought that it was obvious that I was trying to be sarcastic, but today I get an email from my domain registrar telling me that one of my domains has…
-
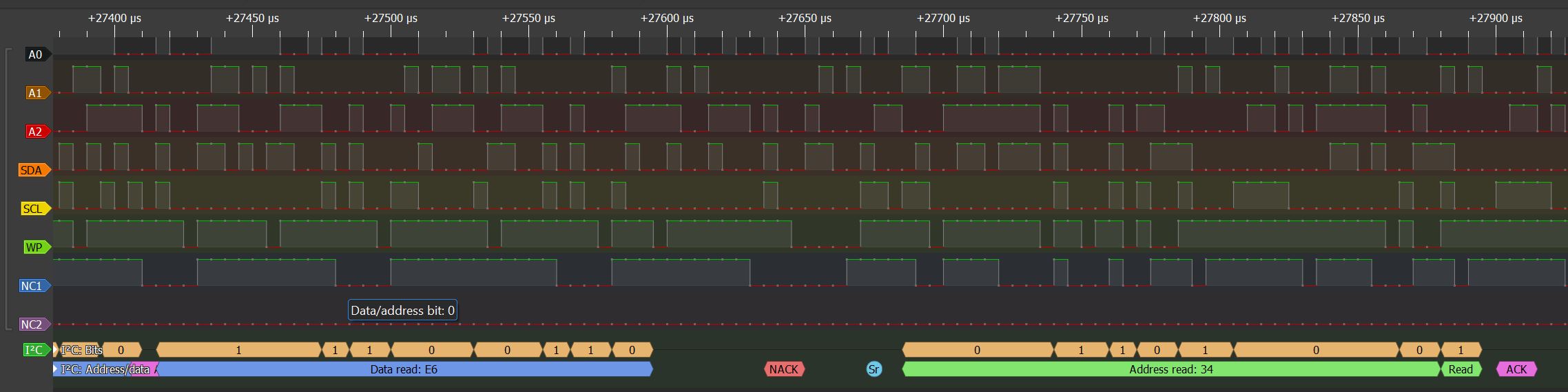
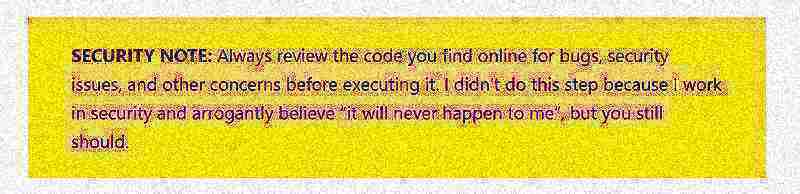
Spying on Chip Communications with Arduino
Recently, I had posted about the faceplate of a safe I had found, got to work, and talked about a method of breaching it. I decided to go a bit further and dump the EEPROM, but the contents of it have (so far) meant nothing to me. I decided it was time to see what…
-

Breaching a Digital Safe
OH LOOK BOB IS GOING TO SHOW US HOW TO USE A MAGNET TO MOVE A SAFE LATCH OR BANG ON IT WHILE PULLING TO HOP A SOLENOID. Not today my friends, but that sure sounds fun, and already done. Most nights, I try to get in a walk. That is, when it isn’t Surface…
-
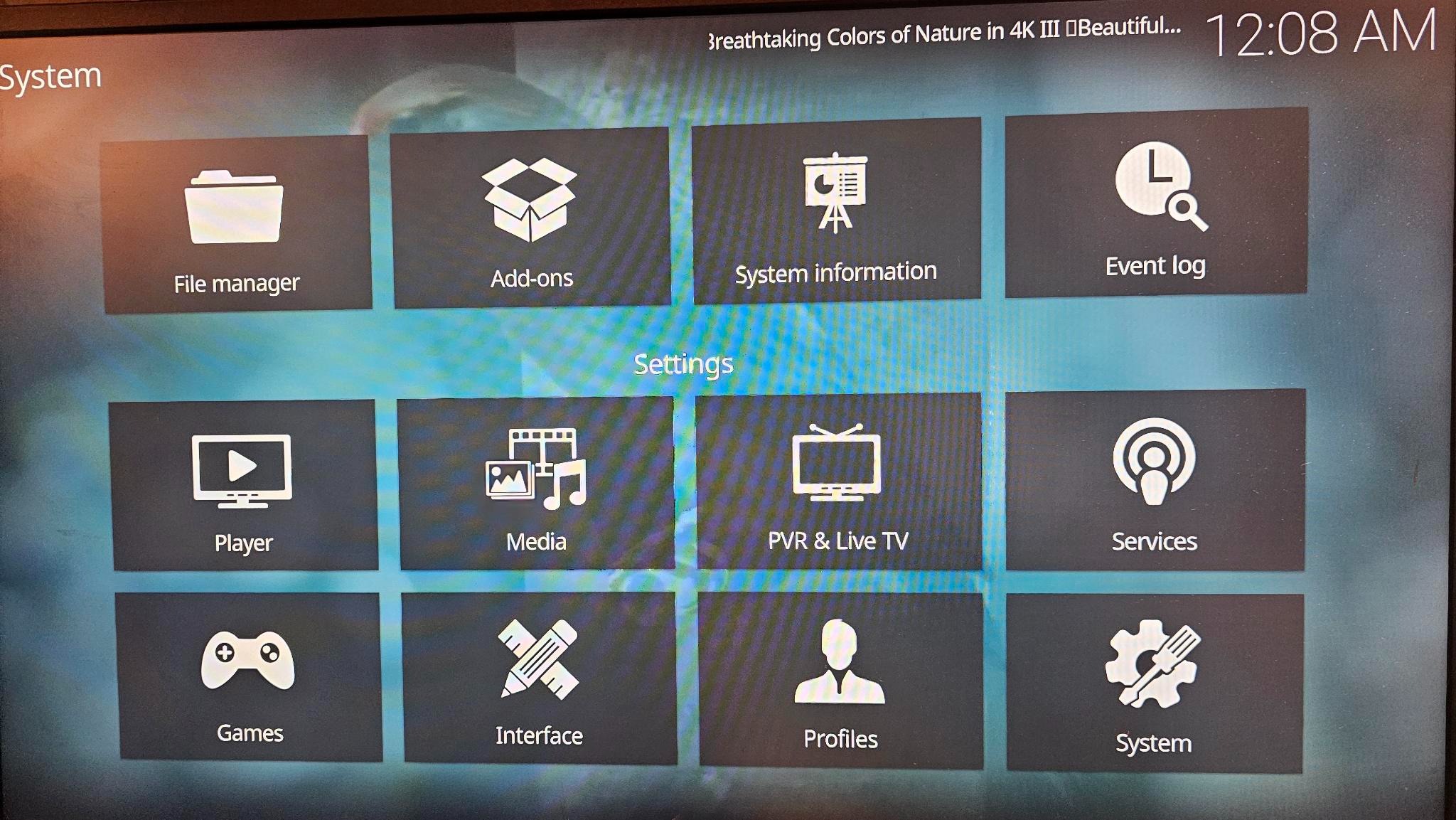
De-FAANG: Replace FireTV, Rokus
PREFACE: I didn’t build the software here and I just followed a series of searches to come up with a solution that meets my needs. You may have different needs and that’s cool too. If you aren’t in an IT related field, this is all we do in this field, search things until one of…
-
De-FAANG: Replacing Echos Part 1
I am not a lawyer or a radio engineer, I can search FCC things and even come up with some convincing understanding of laws, but I don’t have the proper test equipment or background to give this advice, so read it as a fiction novel. Cool, legalese out of the way, I did work for…