Author: rlerner
-

Bye Amazon…For Now
I’ve long been a fan of Amazon, ever since the college I attended for a while wanted ~$75 for a wildly outdated software design book, that I got for less than a dollar from Amazon (paid a few bucks for shipping). I’ve been a customer for almost 20 years, and a Prime member for somewhere…
-

We Should Start Dating
I am thoroughly confident that everybody will leave this blog disgusted. If you meet me for dinner on 23/09/12 at 9,30, I’ll bring the Boone’s farm. This is absolutely in the future. What day is this on? What time? Are you old enough to remember bank deposit forms conveniently filling out the century for you?…
-
Lock your Garage Door
It is likely that you lock your front door, your back door, and you use a deadbolt like you should. You may have even invested in a decent quality lock as well. There’s a few items to consider when breaching a home with an attached garage: If you have a garage door opener in your…
-
My blog has FINALLY MADE IT!
Logged in today to see this!!! Scroll down More More More I didn’t make it.
-
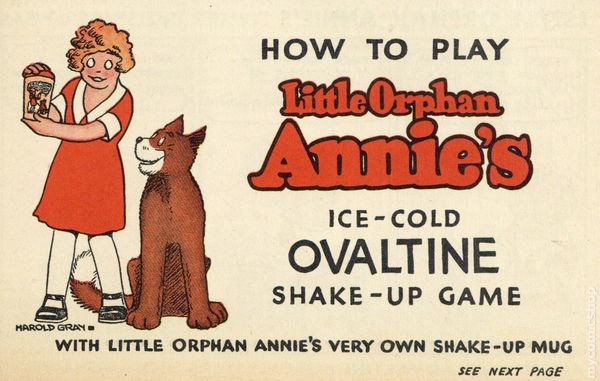
Be Sure to Drink Your Ovaltine
This year marks the 40th anniversary of The Christmas Story, one of my favorite Christmas movies ever made. I don’t think I’m spoiling anything here since this runs 24 hours a day on a ton of stations in December, but if I am, go watch it first. One scene is especially interesting to folks interested…
-
What is my password?
THAT WAY YOU CAN’T SAY IT SUCKS I’ll make more blogs again. Forgot.
-
Profiling LMC Assembly Code
What is Profiling? Profiling is measuring the performance of code, whether it is a small function or an entire application. You can determine how quickly the code will execute various requests and tune them to meet your needs. Cycle Counts The Little Man Computer is easy to do math on, it is 1:1 — one…
-

Little Man Computer – Execution
So far, we’ve learned about the Little Man Computer architecture and how to write a simple program and assemble it into machine code. You likely already know how the code is executed due to the high quality comments I’ve included in that blog. Regardless, I built a simulator and spent quite a bit of time…
-
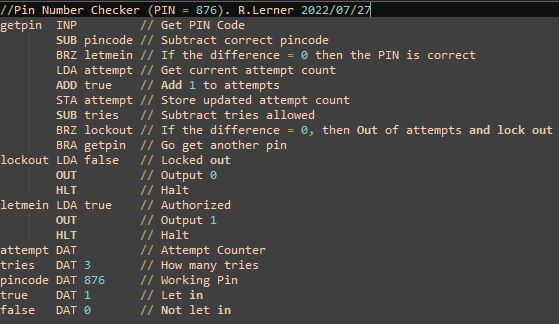
Little Man Computer — Assembly Code
Cover photo isn’t related, but it’s almost as interesting as my post. Machine Code vs. Assembly Code You’ll often hear these two terms used interchangeably, but they are not the same. People will often state that machine code is the actual “0’s” and “1’s” a machine executes, and that’s pretty close to being correct. People…
-
Little Man Computer – Architecture
Around a year ago, I built and threw a Little Man Computer (“LMC”) simulator, assembler, and a really crappy disassembler and put them up on GitHub. There’s another version in C++ up there as well, but it isn’t as fully built out or stable. “Computer Science” in my high school days consisted of keyboarding and…
-

More Locks = More Security?
This morning, I went for a walk and came upon this rather formidable cell tower enclosure. Usually these things are behind a chain link fence — this one is behind a block wall and has a stout gate. After the 2022 substation attack, I can appreciate seeing stronger protection to critical infrastructure. In this case,…
-

Ford Bronco EV Solar Mod
Hi owners of Ford Broncos! This is for the kids ride-on bronco. Sorry! Last Christmas, Santa brought my children something I always wanted — a ride on car! (People call these Power Wheels, but it isn’t a Power Wheels). Around the same time, I was into 3D Printing, and had designed an entire hitch system…