Just yesterday, I posted a blog about spying on chip communications. In there, I included a little tidbit that I “deep fried” here.
Now, I thought that it was obvious that I was trying to be sarcastic, but today I get an email from my domain registrar telling me that one of my domains has been linked to a phishing site, and that I must react within 48 hours. They also obfuscated the domain like this:
hxxp://www.example[.]com
Knowing that this would be a clever way to phish me when I click a link and enter my registrar creds, I went to the registrar direct on a different machine. I didn’t see any notice in there, so I decided I’d check out my domain within a safe VM made for browsing sites.
SECURITY NOTE: I actually used my primary browser on my primary computer, because doing this puts hair on your chest.
Google blocked it saying it was deceptive. So, I go to my registrar’s contact page, which happens to be down at the time … odd.
They did send me a screenshot of what they were seeing:
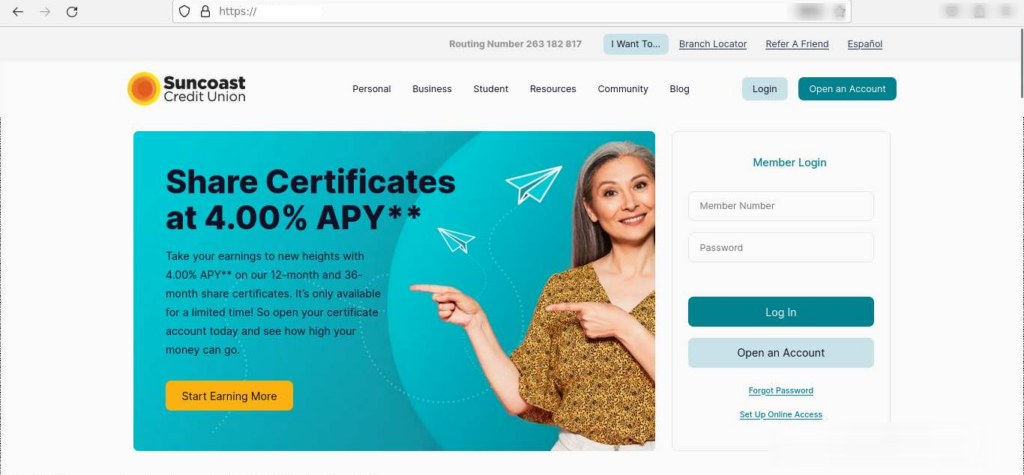
I’ve removed the domain from the screenshot, the blurring on the top was from the registrar, I guess so I can’t tell that they’re using Firefox, and light-mode (gross).
So here’s the background:
- I used to live in Chicago
- I always have liked security since I was pretty young
- Therefore, I had a Chicago-themed security domain
So, I left Chicago for obvious reasons, but I bought the domain for several years, so now I’m stuck with a domain that is clever and also useless to me.
Sometime last year, I went through all my domains I wasn’t using and deleted them from my cloud provider (the files, the virtual hosts, etc).
What I didn’t do was delete the A-records in my registrar to my cloud provider.
How does DNS work?
I’m not going to explain that, grab the RFCs. But what I will do is explain kind-of how it works:
- Internet is made up of “trusted” phone books
- When you visit a site, like robert-lerner.com, these phone books tell the computer the IP Address of the computer that has that site. Remembering IP addresses sucks, remembering hostnames is good.
- The person running the site has to tell the phone book where that IP is
- I told my registrar that the trusted phonebook was at my cloud provider
- Anybody can add any domain to the cloud provider without proving ownership, so somebody else added a record in for my domain name
And made it a phishing site. I’ve corresponded with both companies legal and abuse teams and they’re actively working on bringing down the account that set up the fake DNS pointers and the host of the phishing site. Overall, I think my response time was decent. I was notified at 6:35pm, had DNS updated by 7:04pm (literally a few moments after I noticed the email), and by 8:04pm (due to TTL) the site was down.
Moral of the story?
If you aren’t using a domain, sell it, park it somewhere and make crappy ad revenue, forward it to a new site — but if you’re using a shared DNS host, make sure you either keep a record there, or you get rid of the DNS records within your registrar.
Leave a Reply