Category: Security
-
Scanning IDs — Making Fakes Easier
This is a post from an earlier version of my site, moved to the current version for maximum enjoyment. Originally posted 2018-03-08 -Bob Not long before I procured my wonderful license, they were printed pieces of paper with a photograph attached, then laminated. For both security and durability reasons, all states have moved away from…
-

How to Scam Garage Sale Sites with Gift Cards
PLEASE TAKE NOTE: The title is correct, this is how to scam users of garage sale groups. The intended audience, however, is victims and group administrators. The goal here is to convey how easy it is to defraud people into purchasing gift cards, and why they should not be allowed for sale in these groups.…
-
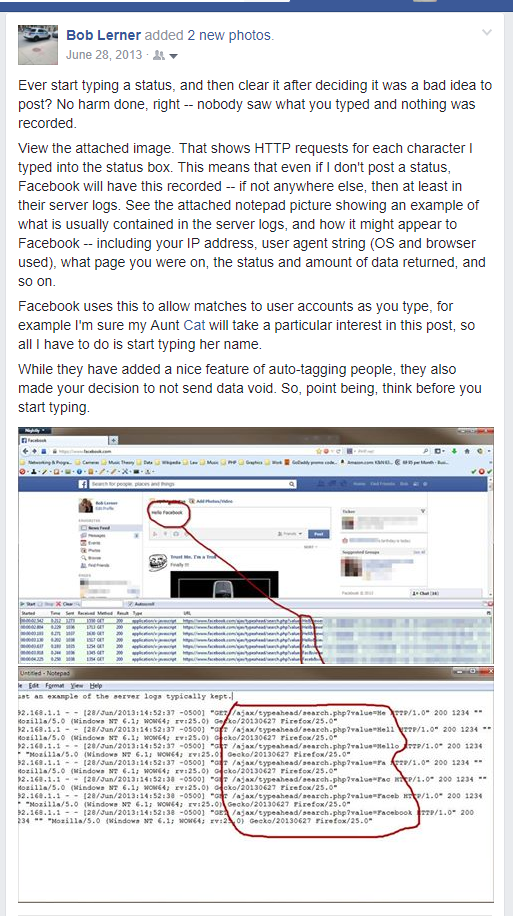
Typed, but didn’t send?
Obviously, this is pretty old. If you’re still using Facebook, the best option is to delete Facebook. That said, this sort of stuff is still valid on most platforms today.
-

Hiding ‘Typing’ and ‘Seen’ from Facebook Chat
This is a very old post of mine from 2012. My advice has STRONGLY changed. Do not do this, in fact, just don’t use Facebook. Don’t use any social networks. They’re terrible and you are the product. I have no idea if this works anymore. Ever get annoyed by people typing “I KNOW YOU SEEN…
-
How-To Securing PHP5 $_GET Strings
This is a VERY old post of mine from 2008 that I’m sharing for sport. There are many articles on the internet, none are complete in securing something. This article is no different. Every day holes are found in code, and they rarely get reported right away…and updated right away. But keeping yourself aware of…